Mobile Platforms Address Data Privacy with 2018 Updates (iOS 12, Mojave, & Android P)
Authors: Gargi Sen, Stacey Gray *
In light of recent debates over Facebook’s role in protecting users’ privacy against third-party app developers, many are recognizing the importance of mobile platforms in safeguarding user data. As the General Data Protection Regulation (GDPR) takes effect in Europe, and initiatives like the California Consumer Privacy Act are debated in America, we will likely continue to see a strong focus on the privacy protections of technology platforms, intermediaries, and operating systems.
Apple emphasized privacy in its Worldwide Developers Conference (June 4-8, 2018), highlighting several privacy-related updates to the upcoming macOS and iOS 12 (described below). The company has also recently updated its App Review Guidelines, clarifying that app developers must respect user privacy – for example, by adhering to a principle of purpose limitation (data collected for one purpose may not be repurposed without further consent) and avoiding certain kinds of behavioral advertising using sensitive information. Google also made privacy a focus of their newest mobile operating system, Android P, with several key software updates that will restrict app developers’ access to user data.
Apple’s Fall Updates
Privacy upgrades coming to iOS 12 and macOS Mojave include:
- Significant Updates to App Store Guidelines: Following the WWDC 2018 conference in early June, Apple made significant changes to its existing App Store Review Guidelines to safeguard user privacy. For example, the updated guidelines bar developers from creating databases from users’ address book information (contact lists and photos). Apps must also have privacy policies, and must request explicit user consent and provide a “clear visual indication when recording, logging, or otherwise making a record of user activity.”
- iOS-Style Permissions for Desktop Apps: MacOS apps will now be required to request the user’s permission to access certain device sensors, such as the camera or microphone.
- Browser Consent Notifications: Safari will prompt browser consent notifications upon detecting website tracking from “Share” and “Like” buttons and website comment feeds. If enabled by default, this will affect social media plugins as well as other interactive features of many websites.
- Prevention of Device Fingerprinting: Safari in macOS Mojave will contain updates designed to prevent device fingerprinting. As FPF described in a 2015 report on cross-device tracking, devices and browsers can be identified with a degree of probability through metadata sent in web traffic – such as the system fonts, screen size, installed plug-ins, etc. This kind of digital “fingerprinting,” often referred to as server-side recognition, is often used for short-term advertising attribution and measurement. In Mojave, the Safari web browser will present websites with a “simplified system configuration,” in order to prevent server-side recognition by making each browser appear more standardized.
- USB Restricted Mode: Although not discussed in the WWDC keynote, an upcoming feature may require iPhone users to input their passcode to unlock the phone when connecting it to a USB accessory if the phone has been locked for an hour or more. This feature would make it much more difficult for an outside entity, such as a government or law enforcement vendor, to unlock a user’s phone without permission.
Google’s Android Fall Updates
Android P, the newest version of Google’s Android mobile operating system, will also bring ambitious updates for user privacy. Many of these updates were announced in May at Google I/O, Google’s annual developer festival. The Android P operating system, which will be available in the Fall, can currently be downloaded in beta form for those who are interested and have compatible devices.
Android P will contain the following updates for user privacy: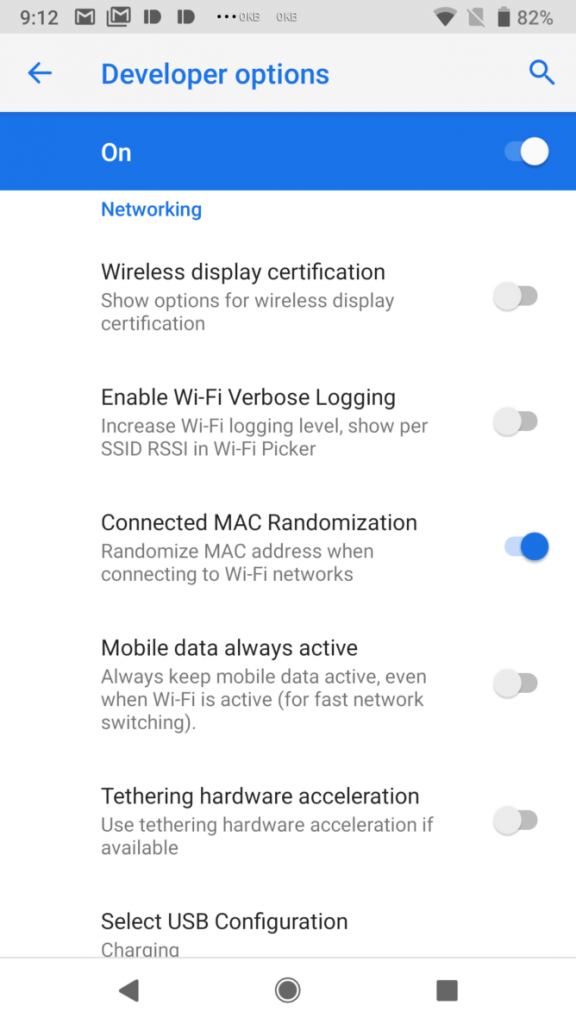
- Restricted Background Access to Sensitive Sensors: If an app is running in the background on an Android P device, the operating system will restrict the apps’ access to the user’s microphone and camera, and will generate an error if an application tries to access them. If an application does need to access these sensors on the phone, it will have to use a foreground service and show a persistent notification on the phone to notify the user of the app’s activity.
- Restricted Access to Call Logs and Phone Numbers: Apps running on Android P can no longer read phone numbers or the user’s call log without first obtaining the user’s in-app permission (similar to location, microphone, or other sensitive sensors).
- Per-Network MAC Address Randomization: Android P has introduced an experimental feature that will generate a different MAC (media access control) address for every Wi-Fi network that the user connects to, making it harder to track individual users. The MAC address is a unique hardware identifier that devices must broadcast in order to connect to Wi-Fi networks. In many physical locations – such as retail spaces, airports, and stadiums – they are used to count and analyze pedestrian traffic. However, because the MAC address cannot be readily changed, privacy concerns around tracking individual users emerged in recent years. In response, operating systems have begun to randomize MAC addresses sent in Wi-Fi “probe requests” (to automatically connect when nearby to a known network). Android P improves on this default and offers users more anonymity by randomizing the identifier even when they are connected to different Wi-Fi networks.
- Location Permission Required for Wi-Fi Scanning: Android P will require apps to obtain the user’s permission to access location information (“ACCESS_COURSE_LOCATION” or “ACCESS_FINE_LOCATION”) before the app may scan for nearby Wi-Fi networks or read Wi-Fi connection information. Many apps facilitate Wi-Fi connections (such as hotspot finders), and in addition, signals from nearby Wi-Fi networks can be used to enhance the accuracy of GPS-based location information. In 2016, the Federal Trade Commission brought an enforcement action against Inmobi, a mobile advertising network, after it was found to be inferring users’ location based on nearby networks even if the users’ had disabled location services.
- Protection of a Unique Identifier: Every Android phone has a unique hardware serial number known as an IMEI, which stays the same through any number of factory resets. Following changes made last year in Android O, app developers can no longer access the IMEI without using a new API (Build.getSerial()), which will provide the serial number only if the developer has obtained the user’s permission to read the phone state.
Importantly, we have seen both Apple and Google take concrete steps this year to enforce their existing developer guidelines. For example, Apple began removing apps from the App Store last month for violations of policies against sharing location data with third party advertisers without users’ consent. Similarly, when security researchers found 36 apps on Google Play that inappropriately collected user data, including geo-location and device information, these apps were removed from the Google Play Store.
These updates to iOS 12 and Android P are an important part of ongoing efforts by mobile platforms to safeguard user privacy and enhance user control. Although operating systems primarily act as data intermediaries – facilitating the user’s interactions with mobile apps of his or her choice – they are also well-positioned to protect users’ expectations. For example, most users prefer that apps be restricted from accessing their geo-location without permission, or using it for secondary purposes beyond what they agreed to or expected. Mobile operating systems can provide these protections and assurances through technical measures and app developer license agreements.
Authors:
Gargi Sen is a Legal Fellow at the Future of Privacy Forum, with 10+ years of experience in technology contracts, compliance, and risk assessments.
Stacey Gray is a Policy Counsel at the Future of Privacy Forum, specializing in Internet of Things, Ad Tech, and geo-location data privacy issues.
Resources:
- Android Developers Blog, Previewing Android P (March 7, 2018)
- Android Developers, Android P Behavior Changes (last updated June 19, 2018)
- Google I/O 2018 (Link)
- WWDC 2018 (Link)
- Apple Developer, App Store Review Guidelines
- Apple Newsroom, Apple introduces macOS Mojave (June 4, 2018)