Showing results for toptout xped xped theft

states-v19 (1)
[…] air travel, or a neighbor forms a negative judgment from gossip. They can also occur when such information is used to commit a crime, such as identity theft or murder.” 81 It is often the use of information that leads to a more tangible kind of harm. For example, if the criminal record of […]

FPF_Always_On_WP
[…] LEGAL CONTEXT 7 HIPAA, 20 and thus subjected to greater regulatory restrictions. Similarly, several states have expanded their legal definitions of personally identifiable information in certain identity theft or breach notification laws to include some form of biometrics. 21 Two states, Illinois and Texas, have broad-reaching statutes that cover biometric data in commercial contexts, […]
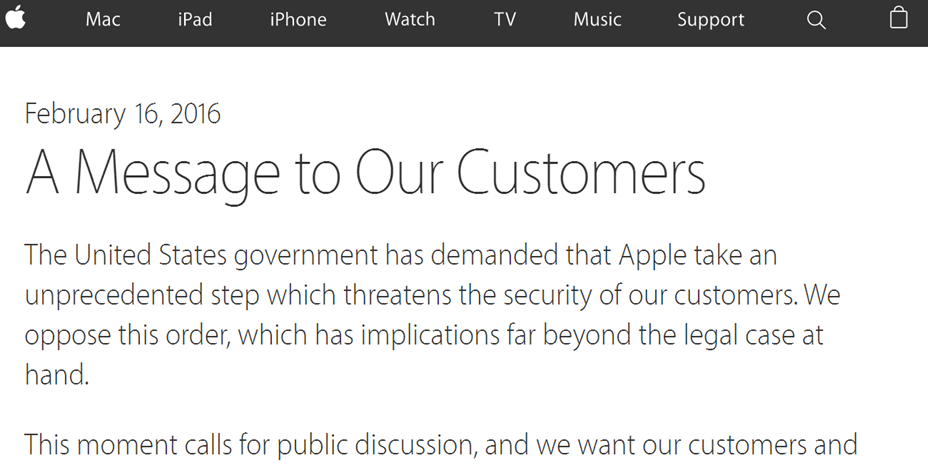
The FBI and the iPhone in Your Pocket
[…] Apple store or if you sent the phone back to Apple headquarters. These protections ensure that your phone is not an easy target for thieves, anymore. iPhone thefts have plummeted by as much as 50% in some cities, after these features were introduced. Unfortunately, the FBI now wants to put the safety of all […]

Privacy Papers 2014
[…] continue to drive privacy debates in 2015. Already in the new year, we have seen the White House push new proposals to address student privacy and identity theft. The Internet of Things has made headlines, moving from something that is coming to something that is here. FPF held a reception to celebrate the release […]

FPF Founder Christopher Wolf wins Vanguard Award
[…] and lectured widely on the subject of privacy law. He is the co-editor of the PLI book, “A Practical Guide to the Red Flag Rules”, those identity- theft-prevention regulations issued by the FTC and financial regulators. He has testified in Congress and before the Privacy and Civil Liberties Board, participated in the 2014 White […]

SwireCrypto070715
[…] It is part of the underpinning of current com m unications netw orks. Indeed, in light of the m assive increase in cyber-crim e and intellectual property theft on-line, the use of encryption should be greatly expanded to protect not only data in transit, but also data at rest on netw orks, in storage, […]

What Privacy Papers Should Policymakers Be Reading?
[…] will continue to drive privacy debates in 2015. Already in the new year, we have seen the White House push new proposals to address student privacy and identity theft. The Internet of Things has made headlines, moving from something that is coming to something that is here. We want to thank EY for their special support […]

FPF_Data Collection and the Connected Car_November2014
[…] – automatically -steers -around -stopped -or-slowin.html. 9 tailored, hands -free experience for using applications in a connected car. 27 Biometrics information could serve as powerful anti – theft protection, as well as providing increased safety and comfort inside the vehicle. In the future, cars will be able to use internal cameras and sensors to […]

Google Taps the YubiKey for Better Account Security
With identity theft and cybersecurity issues in the news seemingly on a daily basis, better tools to protect our data – and our privacy – are always welcome. For some time, FPF has endorsed the use of two-factor authentication as an “extra” step consumers can take to protect their accounts across a variety of online services. While everyone at FPF […]

FPF_NTIA_BigDataPrivacyRFC
[…] were more concerned that their information will be shared for commercial purposes or used to target advertising to them. 9 According to the Federal Trade Commission, identity theft is regularly the top consumer worry, 10 and FTC Chairwoman Edith Ramirez has cautioned that big data will exacerbate the threat posed by data breaches. 11 […]
