Showing results for toptout xped xped theft
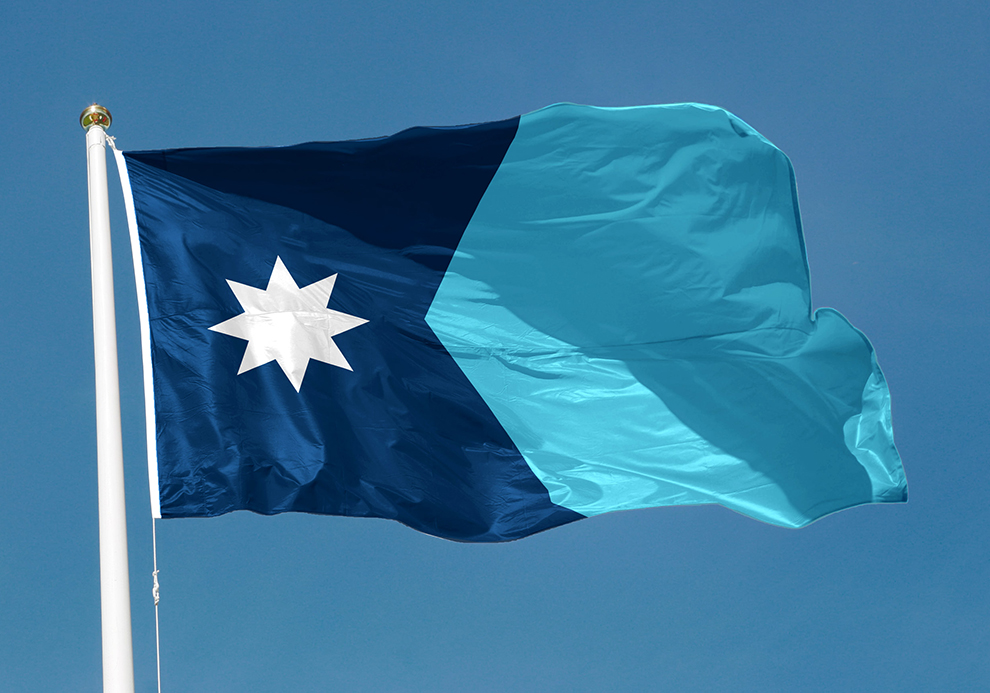
The North Star State Joins the State Privacy Law Constellation
[…] information, this provision arguably narrows the right to access with respect to these types of data, but is likely to benefit security overall and help prevent identity theft. 3. Heightened Data Security Requirements Include Inventorying Data, Documenting Compliance, and Appointing a Chief Privacy Officer Like the majority of states, the MNCDPA requires controllers to […]

FPF Risk Framework for Body-Related Data FINAL Digital
[…] identifiable is typically considered “biometric data.” 65 Biometric data is particularly sensitive because it is inherently tied to each individual, and could be used to facilitate identity theft, security breaches, and personal profiling. Different types of body-related data vary in their identifiability, and it is important to remember that identifiability is not static. For […]

Japan-APPI-Privacy-Notice-2023
[…] cannot be easily accessed by anyone other than employees, etc., who are authorized to handle personal data and the relevant individual. (ii) Measures are taken to prevent theft or loss of equipment, electronic media, and documents that handle personal information. (iii) Measures are taken to ensure that personal information is not easily re vealed […]

Vietnam’s Personal Data Protection Decree: Overview, Key Takeaways, and Context
[…] is needed. This stringent prohibition is a direct response to the numerous cases of personal data misuse that have occurred in Vietnam in recent years, including identity theft, financial fraud, intrusive advertising, and the exploitation of vulnerable individuals. A report showed that in 2022 alone, more than 17 million pieces of personal data were […]

FPF Article 25 GDPR A4 FINAL Digital
[…] that were in quarantine, either due to crossing the country border or a confirmed SARS-CoV-2 infection. In its risk assessment, the company had identified the threat of theft or removal of data by employees or associates. For this reason, it requi red its employees to comply with specific procedures, sign confidentiality agreements, an d […]

Utah Considers Proposals to Require Web Services to Verify Users’ Ages, Obtain Parental Consent to Process Teens’ Data
[…] collecting information beyond what is necessary to provide a service. Requiring social media companies or their agents to collect this data would increase the risk of identity theft resulting from a data breach. We also note that since some social media companies are based outside of the United States (with some located in jurisdictions […]

FPF Playbook singles
[…] environment. » Data loss prevention (DLP) training can help to keep data from being lost through incidents or accidents (e.g., loss of storage hardware like USBs or theft of laptops). Relatedly, research leads should ensure that they ensure effective management of personnel curio sity to prevent “honest but curious” data breach incidents. » Researchers […]

Record Set: Assessing Points of Emphasis from Public Input on the FTC’s Privacy Rulemaking
[…] Many commenters noted that data security incidents are a common occurrence, are not reasonably avoidable by consumers, and pose grave risks to individuals, including that of identity theft. The EDPS underscored the role of data security in protecting core rights and freedoms under EU law and the GDPR, and recommended that the Commission require […]

FPF-Comparative Analysis of CA UK Codes of Conduct R3
[…] compensation for damages suffered. Recital 85 gives several examples of such material or non-material damages: loss of control over personal data or limitation of rights, discrimination, identity theft or fraud, financial loss, unauthorized reversal of pseudonymisation, damage to reputation, loss of confidentiality of personal data protected by professional secrecy or any other significant economic […]

FPF APAC Comparative Review DIGITAL
[…] materialize. Additionally, “significant harm” refers to bodily harm, humiliation, damage to reputation or relationships, loss of employment, loss of business or professional oppo rtunities, financial loss, identity theft, negative effects on credit records, and damage to or loss of pr operty. The Guidelines take a broad view of harm that includes not only harms […]
