Showing results for toptout xped xped theft

Preemption Powerpoint (1)
[…] use my likeness for your advertisement without permission) Property What counts as trespass, eavesdropping? Laws of general application Fraud – every state prohibits this Preempt state identity theft criminal penalties? Every state has UDAP laws ” unfair and deceptive acts and practices” Many non-privacy ways to act deceptively Preempt all state enforcement for deceptive […]

WhitePaper_DataProtectionByProcess
[…] data, to model outputs or the model itself. An adverse outcome could be in the form of both material and nonmaterial damage as a result of identity theft, a form of informational harm. This outcome could happen indirectly when an attacker is able to make inferences about training data through a model inversion attack. […]

ComparingPrivacyLaws_GDPR_CCPA
[…] not provide any figure for potential damages. This remedy is only allowed when non-encrypted or non- redacted personal information is subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the business’s violation of security obligations. Prior to initiating any action against a business for statutory damages on an individual […]

State Legislators Prioritizing Privacy
[…] the Cambridge Analytica scandal, legislators are worried about how user data will be used to influence politics. Following the Snowden revelations and increasing data breaches and identity theft, there has been growing public discontent on the state of privacy protection in the U.S., with the Cambridge Analytica scandal seen by many as the “final […]

A_Taxonomy_of_Definitions_for_the_Health_Data_Ecosystsm_5.29.19_accessible
[…] made to an individual or other entity for services render ed or performed 40 Physical Securities Inspection: Internal investigation of Company incidents involving threats, violence, property damage, theft, and fraud Prevention: The act of reducing the risk of developing disease or other morbidities and minimizing the burden of diseases and associated risk factors Product […]
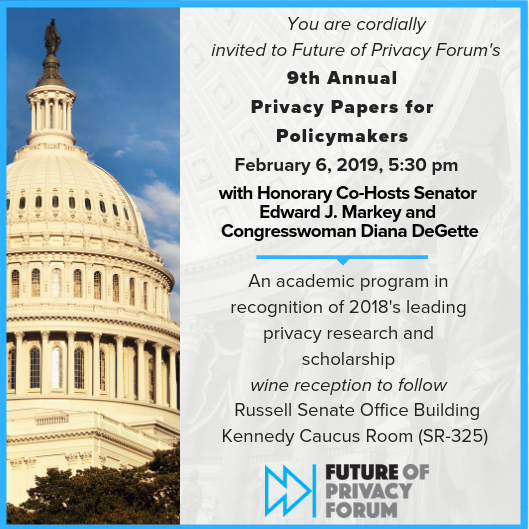
Spotlight on PPPM Finalist Judges (2018)
[…] Lead Author of its first-ever treatise on privacy law. He also is co-editor of the PLI book, “A Practical Guide to the Red Flag Rules”, the identity theft prevention regulations issued by the FTC and financial regulators. John Breyault Vice President of Public Policy, Telecommunications and Fraud, National Consumers League John joined the National […]

GDPR_CCPA_Comparison Guide
[…] objective the protection of data subject rights. This remedy is only allowed when non-encrypted or non- redacted personal information is subject to an unauthorized access and exfiltration, theft, or disclosure as a result of the businessÂ’s violation of security obligations. Prior to initiating any action against a business for statutory damages on an individual […]

FPF-AISP_Nothing to Hide
[…] adequately safeguard data or using it inappropriately can have serious and lasting consequences for individuals. Common privacy risks for individuals include: 13 ›Financial risks, such as identity theft or fraud; ›Physical risks, such as stalking or burglary; ›Reputational risks, such as embarrassing rumors or damaging photos; and ›Dignitary risks, such as a loss of […]

FPF Testifies Before Federal Commission on School Safety
[…] the context of children’s or students’ personal information. Physical harm and loss of liberty are especially egregious when the victim is a child. Financial fraud and identity theft increasingly target young Americans, who are often unable to discover or combat the crimes until years later. Children are also susceptible to specialized schemes – including […]

here
[…] Aᴜᴛᴏᴍᴀᴛᴇᴅ Dᴇᴄɪsɪᴏɴ-ᴍᴀᴋɪɴɢ (Dec. 2017), https://fpf.org/wp-content/uploads/2017/12/FPF-Automated- Decision-Making-Harms-and-Mitigation-Charts.pdf. 6 millions of consumers file complaints each year with the Federal Trade Commission (FTC) alleging that they are victims of identity theft or financial fraud. 14 Inaccurate data can pose risks to individuals’ liberty, with incorrect data in government databases leading to wrongful detention, search, arrest, and incarceration. […]
