Showing results for virg xped sign promo code moldova
NAI Combines Web, Mobile, and Cross-Device Tracking Rules for 2018
The Network Advertising Initiative (NAI) released its 2018 Code of Conduct yesterday, consolidating the rules for online and mobile behavioral advertising (interest-based advertising). NAI, a non-profit organization in Washington, DC, is the leading self-regulatory association for digital advertising, with over 100 members and a formalized internal review mechanism.

The Top 10: Student Privacy News (October-November 2017)
[…] within the tech sector.” A progressive political group “filed FOIA requests seeking the publicly available student directories to get student cell phone numbers at every one of Virginia’s 39 public colleges. Of those, 18 schools, including Tech and Radford, complied.” This will lead to legislation banning directory information disclosures for this purpose next spring. […]

Law Enforcement Access to Student Records: What Is the Law?
[…] Protect Their Students & the Constitution,” Berkman-Klein Center, March 6, 2017. Program to collect information relating to nonimmigrant foreign students and other exchange program participants, 8 U.S. Code § 1372. Retention and Reporting of Information for F, J, and M Nonimmigrants; Student and Exchange Visitor Information System (SEVIS), 67 FR 76255. U.S. Department of […]
Bridging Industry and Academia to Tackle Responsible Research and Privacy Practices
[…] finalized soon) When: November 2 – 3, 2017 Location: Facebook Offices, 770 Broadway, New York, NY To encourage a diverse set of attendees, we ask those who are interested to provide their resume or CV and a 1 to 2-page submission. Please click the link below for details. READ MORE Wooden sign with ethic concepts

WannaCry About Backdoors
[…] Shadow Brokers. An initial lesson is to remind us that leaks can and do happen from intelligence agencies, from Edward Snowden, through the publication of CIA hacker code, to the Shadow Brokers release of NSA hacker tools. In an era where leaks happen at scale and get disseminated globally, agencies face a “declining half […]

Privacy Scholarship Research Reporter: Issue 1, May 2017 – Algorithms: Privacy Risk and Accountability
[…] algorithms often operate on a random group-level, which may pose additional difficulties when interpreting and articulating the risks of algorithmic decision-making processes. In light of the possible significance of the impact on human beings, the complexities and the broader scope of algorithms in a big data setting call for accountability mechanisms that transcend the […]

The Top 10: Student Privacy News (Feb-March 2017)
[…] & What School Decision-Makers Can Do to Protect Their Students & the Constitution.” States and districts continue to worry about potential ICE requests of student immigration status data. You can sign up to attend a March 30th webinar discussing “The Educational Rights of Immigrant Children.” In the meantime, lawyers have been pouring over US Code to figure […]
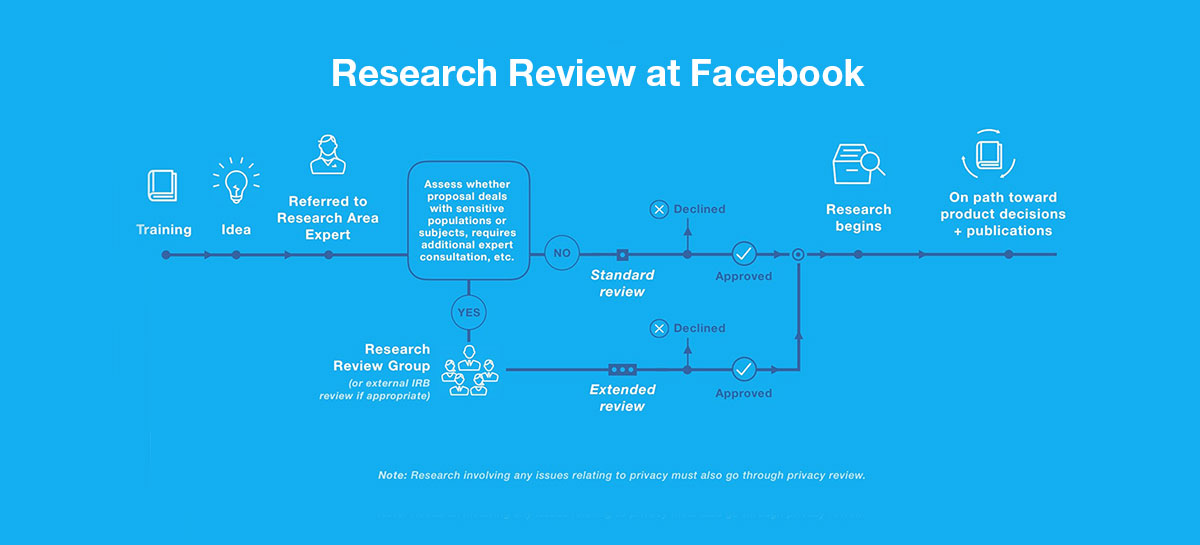
Examining Ethics, Privacy, and Research Reviews
[…] Jackman’s paper documenting the Facebook research process provides researchers with a valuable model for serious evaluation of the benefits and risks of new projects.” PAPERS Read Facebook’s paper Read Facebook’s blog Read Jules Polonetsky’s and Dennis Hirsch’s joint op-ed in Re/ code Read Beyond IRBs: Designing Ethical Review Processes for Big Data View event photos

June 14th Event: A Roundtable on Ethics, Privacy, and Research Reviews
[…] 2016 from 9:30 am to 12:30 pm (EDT) – Add to Calendar WHERE Future of Privacy Forum – 1400 I Street Northwest Suite 450, Washington, DC 20005 – View Map PAPERS Read Facebook’s paper Read Facebook’s blog Read Jules Polonetsky’s and Dennis Hirsch’s joint op-ed in Re/ code Read Beyond IRBs: Designing Ethical Review Processes for Big Data

Always on: Privacy Implications of Microphone-Enabled Devices
[…] the primary way to interact with devices enables companies to collect, store and analyze increasing amounts of personal data. But consumers don’t always understand when and in what ways these devices are actually collecting information. Additional Resources Read the full op-ed in Re/ code Read the article in CheatSheet Read the press release Download paper
